Hello World,
In this post, I will continue to summarize the issues our user community has been facing while using our wonderful, on-the-edge remoteapp infrastructure. This post will be quite short as well.
So, let’s start this…
The problem
The Access denied situation was affecting standard users as well as administrators personnel. The symptoms looked the same as the one described in this post. So, when a user was trying to launch a remoteapp from the web interface, the remote session connection would start but after a while an access denied message would be displayed.
We checked a bunch of settings related to remoteapp before moving to the next potential suspect… KERBEROS
The Solution
As you would have guessed, the access denied message we were receiving was not related to settings of the RemoteApp infrastructure but more related to the kerberos authentication. Going through event viewer > System logs, we have quickly identified the error. Kerberos token of the users were oversized. In event viewer, you should see a message “similar” to the following one….
Source: Kerberos Event ID: XX Type: Warning Description:The Kerberos SSPI package generated an output token of size 12589 bytes, which was too large to fitin the token buffer of size 12000 bytes, provided by...The application needs to be fixed to supply a token buffer of size at least 65530 bytes.
To solve the issue, you would need to either check if one of the admin has added users to a new group (with a lot of nesting) which would then explain why suddenly all your users have the problem. The other option is to increase the maxTokenSize value on each computer.
You can modify the value of the MaxTokenSize via registry by navigating to the following location
HKLM\System\CurrentControlSet\Control\Lsa\Kerberos\Parameters
Either the MaxTokenSize already exists and you adapt the value to max 65 535 or you created a REG_Dword object and set the value also to maximum 65.535. Above this value, kerberos authentication process might fail with other applications. Microsoft recommends to set the value of maxTokenSize to 48 000.
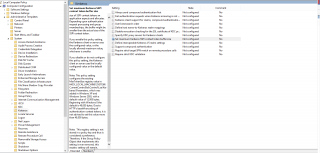
If you have the problem through all your organization, note that you can use a Group Policy to adjust the Max Size of the token. When you create your gpo, you can on computer>System>Kerberos and you will find the setting “set maximum kerberos SSPI context token buffer size”
Click on Pictue for better Resolution
Set the value that you want to have and you are ready to go…. Do not forget to have client updating their gpo so this setting would apply
Final Notes
This kerberos issue let us remind us that Remote Desktop Services is tightly integrated with Active Directory and relies on Kerberos authentication. Because we had previously this error in other projects, we were able to quickly identify the issue. In some organizations, this debugging process can take some time and let your uses un-happy because they cannot use your nice and shinning remoteApp infrastructure.
I hope that you have found this post useful.
Till next Time
See ya
References about MaxTokenSize in Windows 2012/Windows 8 :